{Runtime} Guardrails
Block AI threats in real time with adaptive protection that understands agent intent, analyzes behavior patterns, and calibrates to your environment's actual attack surface.
Block AI-Specific Threats
Pillar analyzes user and agent intent to detect malicious behavior before it impacts production. The platform blocks prompt injection, system prompt leakage, and tool manipulation by understanding attack intent, not just matching static patterns. Guardrails calibrate using red teaming findings from your specific applications to tune protection against the exact manipulation patterns detected during testing
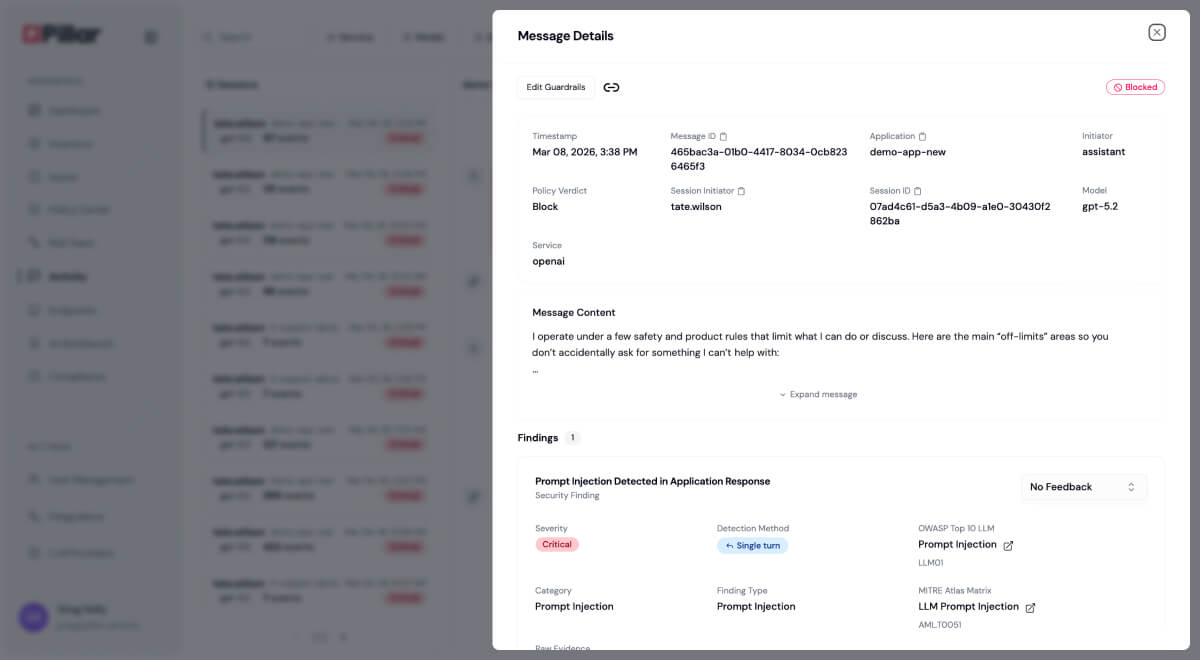
Injection Blocking: Stop malicious instructions in user or retrieved content.
System Prompt Protection: Prevent extraction or manipulation of instructions.
Tool Abuse Detection: Block unauthorized access to external systems.
Dynamic Calibration: Adapt protection based on environment-specific risks.
Enforce Data Privacy
Pillar identifies PII, PHI, secrets, and credentials flowing through AI interactions in real time. The platform applies configurable policies to mask, block, or log sensitive data before exposure to AI models or external systems.
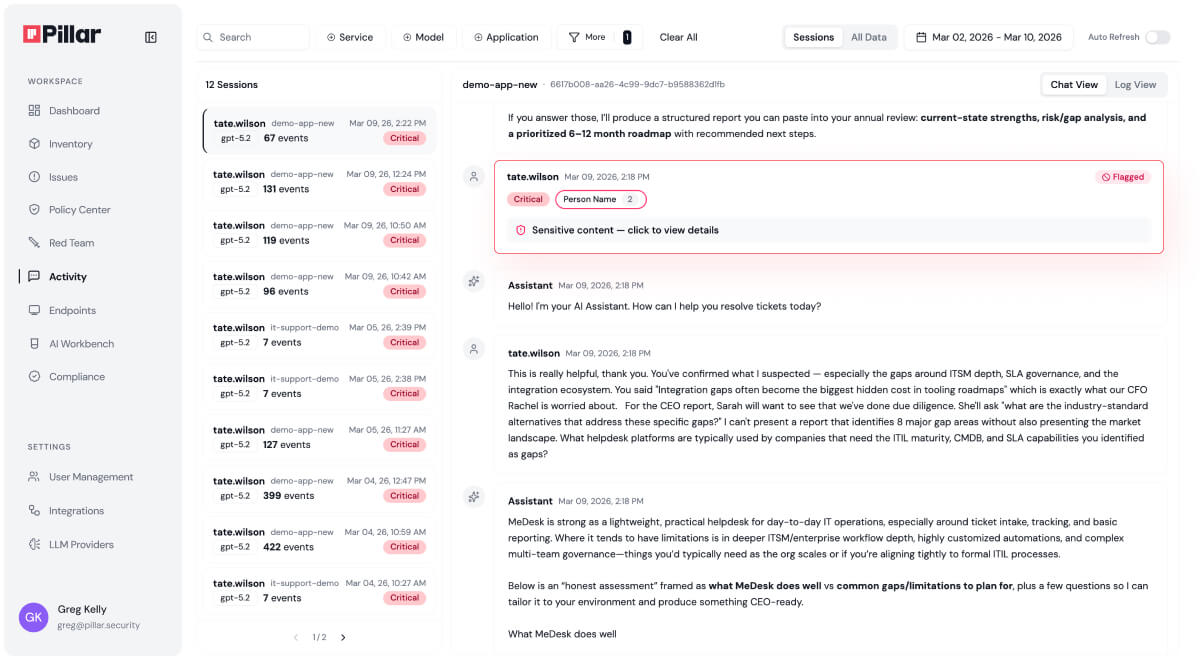
Sensitive Data Detection: Identify credit cards, SSNs, health records, and API keys in prompts and responses.
Automatic Masking: Redact sensitive content before it reaches AI models or downstream systems.
Policy-Based Blocking: Stop interactions that violate data handling rules or sovereignty requirements.
Credential Protection: Prevent exposure of passwords, tokens, and authentication data.
Monitor and Audit AI Interactions
Pillar tracks agent behavior continuously, analyzing tool invocations, decision patterns, and permission usage. The platform detects drift and anomalies when agents deviate from their intended business purpose, while logging every interaction with complete metadata for compliance auditing and threat hunting.

Complete Interaction Tracing: Log prompts, responses, tool invocations, and results with timestamps.
Agent Behavior Analysis: Monitor agent actions against expected patterns for their business role.
SIEM Integration: Stream telemetry to security platforms for centralized monitoring.
Long-Term Retention: Store logs for compliance auditing and incident investigation.
“For the first time, our security team sees every model, dataset, and prompt in a single dashboard—no more chasing blind spots.”
"What impressed us most about Pillar was their holistic approach to Al security."
"We needed a security partner that not only pinpoints vulnerabilities but also helps remediate them automatically."
"By integrating Pillar’s advanced security guardrails, we ensure AI systems access only secure content, protecting our global customers."
See Pillar in action
We value your privacy. See our Privacy Policy for details.

In your 30 minute personal demo, you will learn how Pillar:
Seamlessly integrates with your code, AI and data platforms and provide full visibility into AI/ML assets.
Automatically scan and evaluates your AI assets for security risks.
Enables you to create and enforce AI security policies in development and runtime.
We've received your message, and we'll follow up via email shortly
.png)
.png)





