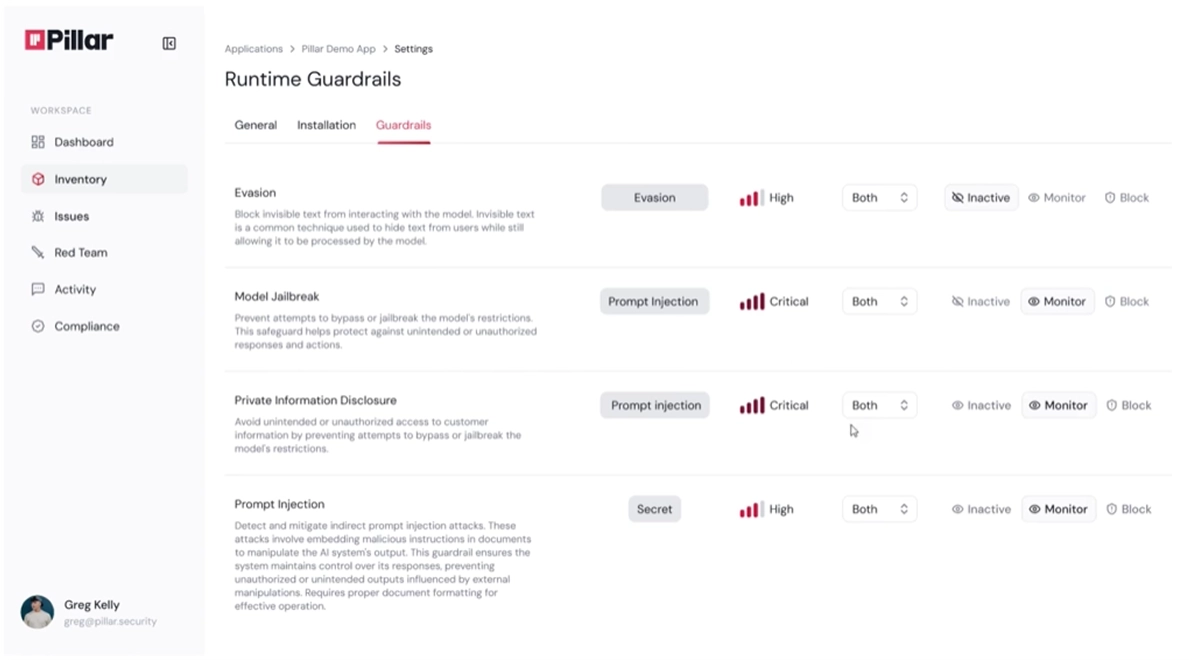
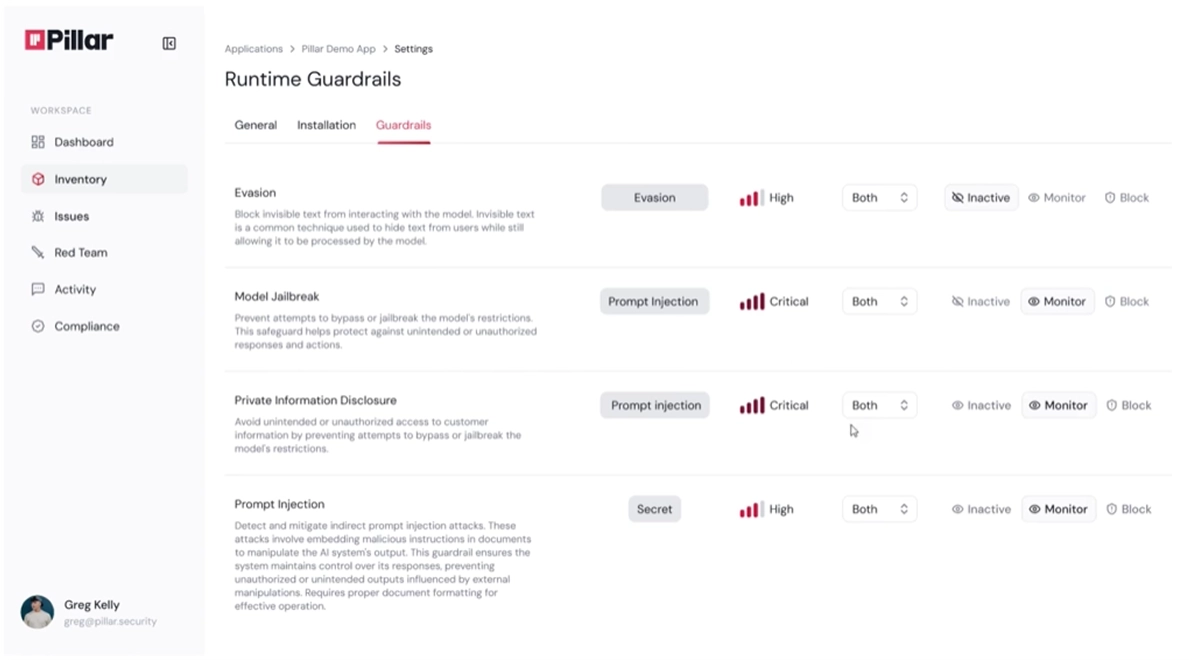
{Runtime} Guardrails
Dynamically catalog AI assets in your organization, map dependencies, and assess security posture across your entire AI stack.
Discover Every AI Asset
Pillar flags violations when unsanctioned AI appears in your environment. PolicPillar catalogs agents, models, prompts, tools, MCP servers, and coding agents through agentless integrations with source code repos, data platforms, and endpoints. The platform detects shadow AI across your organization, identifying unauthorized systems as teams deploy them Pillar enabled the adoption of safe AI usage by enforcing policies on approved AI assets.y rules enforce approved models, frameworks, and data sovereignty standards across your AI stack.
Agentless Integration: Connect to repos, data platforms, and endpoints without agents
Continuous Scanning: Detects new AI systems as teams deploy them
Shadow AI Detection: Identify unauthorized models, coding agents, and MCP servers
Business Context Mapping: Link assets to owners, departments, and data sensitivity
Enforce Approved AI Policy: Define and maintain a unified approved AI policy across multiple assets
Assess Security Posture
Pillar assesses risks in your AI stack from vulnerabilities in models, frameworks, and dependencies. The platform prioritizes findings based on business impact and exposure, mapping them to industry standards.
Supply Chain Analysis: Trace dependency chains and validate model provenance
Vulnerability Detection: Identify security flaws in AI components and integrations
Risk Prioritization: Rank findings by severity, business context, and exploitability
Posture Tracking: Pillar integrated with ticketing and operational system to alert on critical issues demanding immediate response
Enforce Policy and Governance
Pillar flags violations when unsanctioned AI appears in your environment. Policy rules enforce approved models, frameworks, and data sovereignty standards across your AI stack.
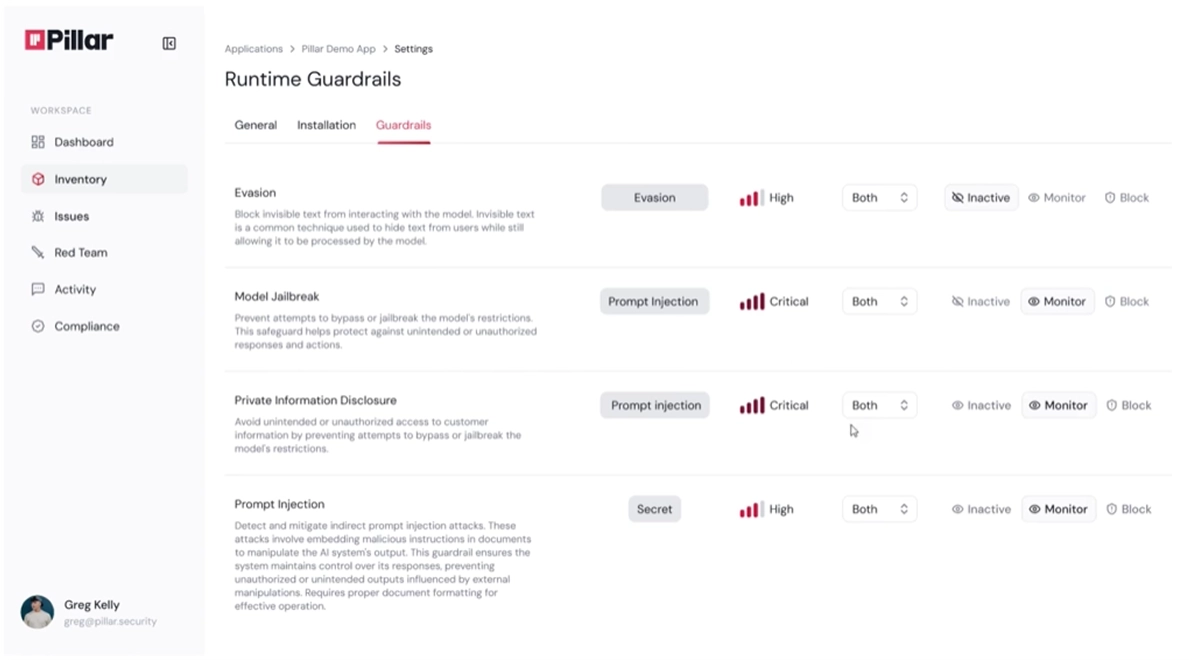
Automated Policy Enforcement: Block and track unapproved models and stop them from being deployed
Compliance Mapping: Generate audit reports for GDPR, SOC 2, EU AI Act, and ISO 42001
Real-Time Alerting: Receive notifications when policy violations occur
Remediation Workflows: Trigger automated responses to policy breaches
“We have numerous AI initiatives throughout the company. Unlike traditional red teaming, RedGraph helps us identify critical risks in our AI agents by fully mapping and understanding their attack surface, providing proven attack paths that the engineering team can fix immediately. This marks a significant improvement in our security measures.”
“Prior to RedGraph, our adversarial AI teams were bottlenecked by limited, manual tools. Now, we launch end-to-end security assessments at massive scale. The exploit validation is a game changer. When engineers see the actual attack path, there's no debate about severity or priority.”
See Pillar in action
We value your privacy. See our Privacy Policy for details.

In your 30 minute personal demo, you will learn how Pillar:
Seamlessly integrates with your code, AI and data platforms and provide full visibility into AI/ML assets.
Automatically scan and evaluates your AI assets for security risks.
Enables you to create and enforce AI security policies in development and runtime.
We've received your message, and we'll follow up via email shortly




